"I’ve spent my entire career teaching companies how to protect their most valuable assets from intruders. I build firewalls, I encrypt data, and I hunt for vulnerabilities. I thought I had built a perfect life with a perfect woman in a perfect, secure home. But what they don't tell you in cybersecurity school is that the most dangerous Trojan Horse isn't a piece of code—it’s the person you let through the front door with a kiss and a key."
My name is Ethan. I’m thirty-two, and I’m a senior cybersecurity consultant. My life is defined by logic, patterns, and access control. Two years ago, I bought my dream home—a sleek, three-bedroom modern craftsman in a quiet suburb. Being a tech nerd, I didn't just buy a house; I built a fortress. Every light, every lock, every speaker, and every sensor was integrated into a central hub I coded myself. I could see the temperature of my toaster from a hotel room in Singapore if I wanted to.
Then there was Tara.
Tara was twenty-six, vibrant, and had this way of making my cold, logical world feel warm. We’d been together for eighteen months. She wasn't a "tech person"—she used to joke that my house was "haunted" because the lights would dim automatically when we started a movie. I loved that about her. I thought her simplicity was the perfect balance to my complexity.
She lived with me about five days a week. Her presence was everywhere. Her expensive French candles on my marble countertops, her silk robes in my closet, and that specific scent of vanilla and jasmine that seemed to cling to the walls. I trusted her with everything. I gave her the master access code to the house. I gave her my heart.
But about three months ago, the patterns changed.
In my line of work, you learn to spot anomalies. A sudden spike in data usage, a login from an unrecognized IP—or in Tara’s case, a sudden, frantic interest in my travel schedule.
"Ethan, babe, remind me again... what time is your flight to Denver on Tuesday?" she asked while picking at her salad.
"6:00 AM," I replied, not looking up from my laptop. "I’ll be back Friday night. Why? Planning a surprise?"
She laughed, but it was a bit too high-pitched. "No, just wanted to know when I should have dinner ready for your return. I’m going to miss you so much."
The red flags started waving. She began sleeping with her phone under her pillow. She started taking "work calls" on the patio at 11:00 PM. But I loved her, so I did something a cybersecurity expert should never do: I ignored the data. I chose to believe the person, not the patterns.
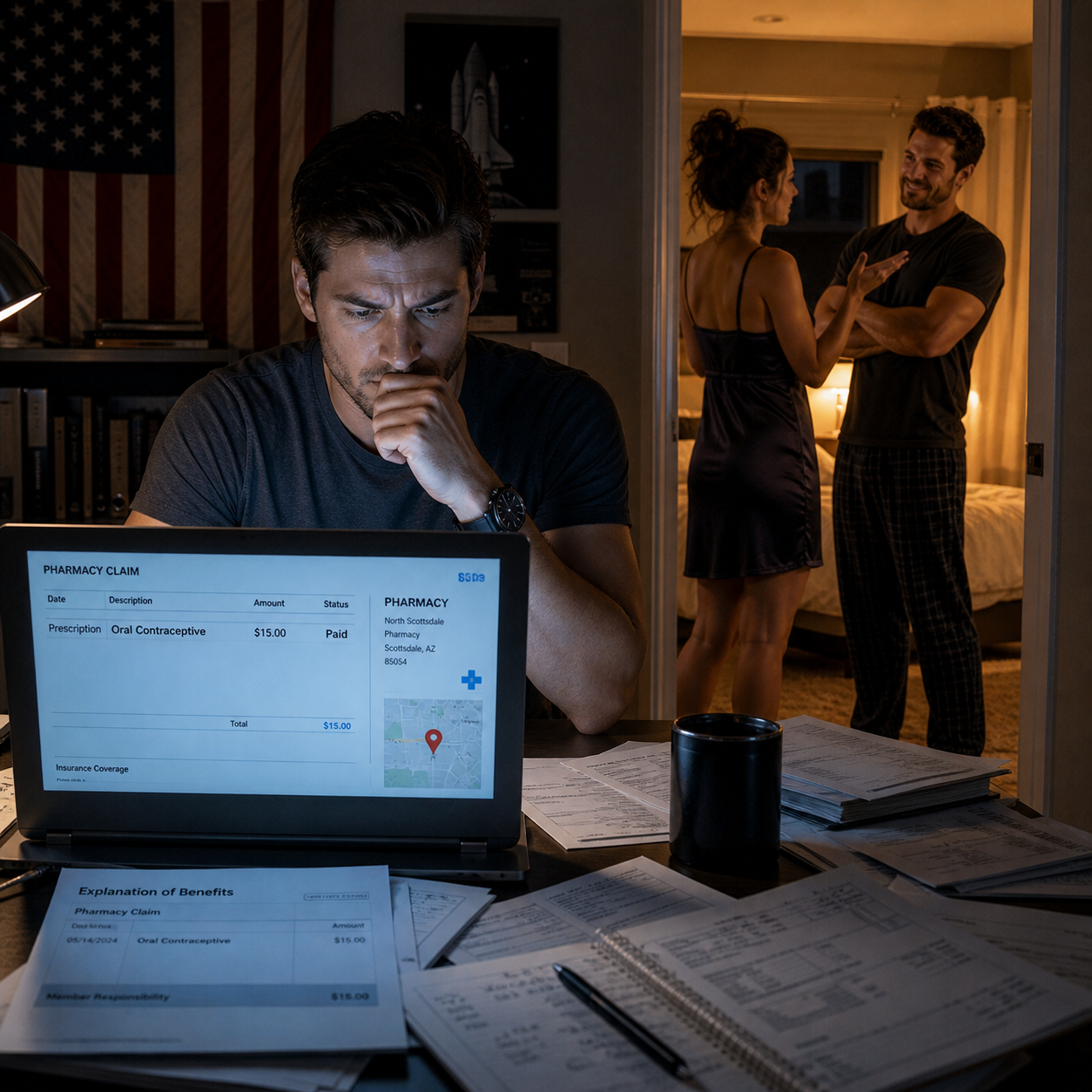
Tuesday morning came. I kissed her goodbye, smelling that vanilla scent one last time, and headed to the airport. By 10:00 PM, I was in my hotel room in Denver, the city lights blurred by the rain on the window. I opened my laptop to finish a report, but my finger hovered over the bookmark for my home security dashboard.
Just a quick check, I told myself. To make sure the perimeter is set.
The dashboard loaded. I clicked on the living room feed. My heart stopped.
The lights were set to "Evening Ambience"—a 20% amber glow I usually reserved for our date nights. There was music playing—I could see the waveform on my audio output monitor. And there, on my Italian leather sofa, was Tara.
She wasn't alone.
A man—tall, muscular, wearing a fitted shirt that probably cost more than my first car—was sitting next to her. They were laughing. They were drinking a bottle of my 2012 Cabernet. The one I was saving for our two-year anniversary.
I watched, paralyzed, as he leaned in and whispered something in her ear. She tilted her head back and laughed—that same laugh she gave me when I told her I loved her. Then, she reached out, grabbed his collar, and pulled him into a kiss.
It wasn't a "mistake" kiss. It was a "we’ve done this before" kiss.
I felt a physical pain in my chest, like someone had reached in and short-circuited my ribs. I wanted to scream. I wanted to call her and melt the phone with my rage. But then, the professional in me took over. The hunter.
I didn't close the feed. I watched. I watched them move to the kitchen. I watched her show him how to use my high-end espresso machine. I watched him put his hands on her waist while she stood at my counter—the counter I paid for, in the house I built.
She looked at the camera in the corner of the kitchen. She knew it was there. But she also knew I "never checked it unless the alarm went off." She felt safe. She felt invisible.
I realized then that Tara didn't just want another man; she wanted my life, my resources, and my home to facilitate her betrayal. She was using my own fortress to hide her siege.
I spent the rest of the night staring at the screen, my mind spinning. I could have disabled her code right then. I could have set off the sirens and called the police. But that was too simple. Too quick.
I needed her to understand the gravity of what she had breached. I needed her to realize that in this house, I was the one who controlled the reality.
I began writing a script. Not a movie script, but a sequence of commands for my home automation system. A sequence I titled: "The Firewall."
The next morning, Tara texted me: "Morning handsome! Just woke up, the bed feels so empty without you. Can't wait for you to be home Friday. Love you!"
I stared at the message, a cold, dark smile spreading across my face. I replied: "Love you too, babe. Change of plans—flight is delayed. I won't be back until late Friday night, maybe even Saturday morning. Don't wait up."
I saw the "Typing..." bubble appear instantly.
"Oh no! That's okay, I'll just have a quiet night in. Take your time, work hard!"
She was excited. She was clearing the schedule for Round Three. But as I sat in that Denver hotel, I wasn't sad anymore. I was focused. She thought she was the one playing the game, but she had forgotten one fundamental rule of cybersecurity:
Never try to outsmart the person who built the system.
But as I began to pack my bags for an early, secret flight home, a notification popped up on my screen that made my blood run cold. It was a request for a secondary guest access code, generated from my own kitchen tablet... and it was for a name I recognized from her past.


![[FULL STORY] He Kicked Me Out In The Rain… He Didn’t Know The House Was Never His](https://sa.greatgames.info/storage/thumbnails/1776737589_D60.jpeg)
![[FULL STORY] She Said “It Wasn’t Cheating Yet” — So I Exposed Her at the Altar](https://sa.greatgames.info/storage/thumbnails/1777127758_b2b5fdc3-81e2-48dc-9f5d-648ea6c250ad.png)

![[FULL STORY] At Dinner, She Announced: “This Is the Longest I’ve Stayed True ” The Room Burst into Laughter](https://sa.greatgames.info/storage/thumbnails/1776920856_24.png)